If you’re a WordPress enthusiast, you know the thrill of discovering great plugins to enhance your website’s capabilities. Ninja Forms stands out in this regard, offering users a simplified way to create dynamic forms. But like many tech tools, security issues can emerge, and it seems Ninja Forms has found itself in such a position again.
The latest buzzword in the web security community? CVE-2026-0740. It sounds like tech jargon from a sci-fi movie, but it’s the identifier for a notable vulnerability in Ninja Forms. This flaw could potentially expose websites to malicious activity, affecting not just web admins but also visitors.
In this post, we’ll unravel the details behind CVE-2026-0740, diving into how it was discovered, its potential risks, and the steps you can take to protect your site. Whether you’re a seasoned developer or a casual blogger, understanding this vulnerability is crucial in safeguarding your digital space.
Stay tuned as we explore the ins and outs of this vulnerability and provide actionable insights on fortifying your WordPress site against future threats.
Understanding the Ninja Forms Vulnerability
Navigating the world of WordPress plugins means always keeping an eye on security. The recent vulnerability in Ninja Forms, identified as CVE-2026-0740, is a crucial reminder of why vigilance is key.
What is CVE-2026-0740?
CVE-2026-0740 sounds complex, but it essentially refers to a specific security flaw in the Ninja Forms plugin. This vulnerability originates from improper input validation, meaning that it fails to correctly check data being entered or processed. Hackers could exploit this flaw to inject malicious code, potentially gaining unauthorized access or causing disruptions.
While the Ninja Forms team is renowned for their quick responses to such issues, awareness and action from users play a big role in preventing breaches.
Impact on WordPress Users
For WordPress users relying on Ninja Forms, this vulnerability serves as a major alarm bell. It opens the door to potential data breaches, unauthorized access, and loss of control over form entries. For businesses, this could mean compromised customer data, leading to trust issues and, in worst-case scenarios, legal repercussions.
Even personal blogs aren’t immune. Sensitive visitor information could be exposed, making it vital for all users to assess their security measures. Early detection and prompt updates are key strategies in mitigating these risks and maintaining a secure online environment.
Technical Details of CVE-2026-0740
Getting into the nitty-gritty of CVE-2026-0740 helps us understand the scope and severity of the vulnerability. Here’s a closer look at how this exploit functions and which versions of Ninja Forms are affected.
How the Exploit Works
At the heart of this vulnerability is a flaw in the input validation process. When a user inputs data into a form, Ninja Forms should verify that the data is safe and expected. However, CVE-2026-0740 presents an opportunity for attackers to bypass these checks. By injecting malicious scripts or SQL commands through form fields, an attacker can take control over certain functionalities of the website.
This means unauthorized players could manipulate data, steal sensitive information, or even hijack parts of your site, all without attracting immediate notice.
Affected Versions of Ninja Forms
Identifying which versions of Ninja Forms are impacted is critical for taking timely action. CVE-2026-0740 is known to affect versions 3.5.0 through 3.5.12. If your website is running any of these iterations, it’s crucial to update to the latest secure release as soon as possible.
Staying updated with the latest plugin versions is not just a matter of functionality, but of security itself. Always check for updates and apply them promptly to minimize potential risks.
Steps to Mitigate the Vulnerability
Addressing CVE-2026-0740 requires a proactive approach to secure your WordPress site. Let’s explore the steps to safely update Ninja Forms and general security measures you should adopt.
Updating Ninja Forms Safely
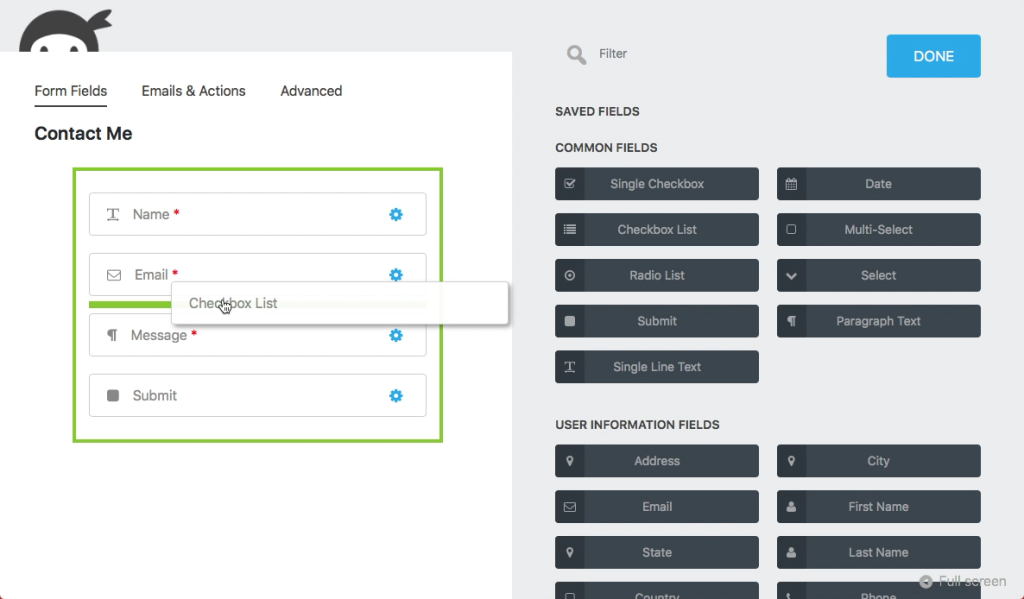
First things first—if you’re using an affected version of Ninja Forms, updating is essential. Visit the plugins section of your WordPress dashboard, find Ninja Forms, and check for any available updates. Alternatively, directly download the latest version from the WordPress repository.
Before you hit that update button, back up your site. Ensuring you have a current site backup protects you from any unforeseen hitches during the update process. Once backed up, proceed with the update to close the vulnerability.
Security Best Practices
Beyond updating, there are other security best practices to maintain a robust defense. Regularly scan your site with a reliable security plugin to catch vulnerabilities early. Limit the number of administrators and use strong, unique passwords.
Keep all plugins and themes updated consistently, and consider enabling auto-updates for essential ones. Additionally, implementing a web application firewall can provide an extra layer of security, guarding against unauthorized access attempts.
By maintaining a vigilant security routine, you can significantly reduce the risk of vulnerabilities affecting your WordPress site.
Conclusion
Reflecting on the latest vulnerability in Ninja Forms highlights a universal truth about technology: staying informed and proactive is key to maintaining digital security. CVE-2026-0740 serves as a reminder of the dynamic nature of threats that can affect our online spaces.
Ensuring WordPress Site Security
Securing your WordPress site goes beyond just addressing individual vulnerabilities. It’s about embracing a holistic approach to security. Regular updates, vigilant monitoring, and educated user practices form the pillars of a robust defense system.
By integrating strong passwords, limiting admin access, and utilizing security plugins, you’re creating multiple layers of protection. Don’t underestimate the power of community and resources available to WordPress users—engage with forums, follow security bulletins, and leverage support when needed.
In the ever-evolving digital landscape, the commitment to security is an ongoing journey. With diligence and the right tools, you can ensure that your WordPress site remains a safe and trusted platform for both you and your visitors. Keep learning, stay alert, and reinforce your defenses to navigate the challenges of tomorrow’s web securely.




