Recently, a significant vulnerability labeled CVE-2026-33032 was identified in the Nginx UI, raising concerns across the tech landscape.
This vulnerability posed a potential risk to countless servers, potentially leaving sensitive data exposed. Thankfully, the Nginx team acted swiftly, rolling out a security patch to safeguard users from possible exploitation.
In this blog post, we’ll delve into what CVE-2026-33032 is all about, who it affects, and how the Nginx UI patch effectively counters this looming threat. We’ll also explore steps you can take to ensure your systems remain safe and secure.
Whether you’re an IT professional, a web developer, or simply a tech enthusiast, understanding these vulnerabilities and the industry’s response is key to maintaining robust cybersecurity defenses.
Understanding CVE-2026-33032
What is CVE-2026-33032?
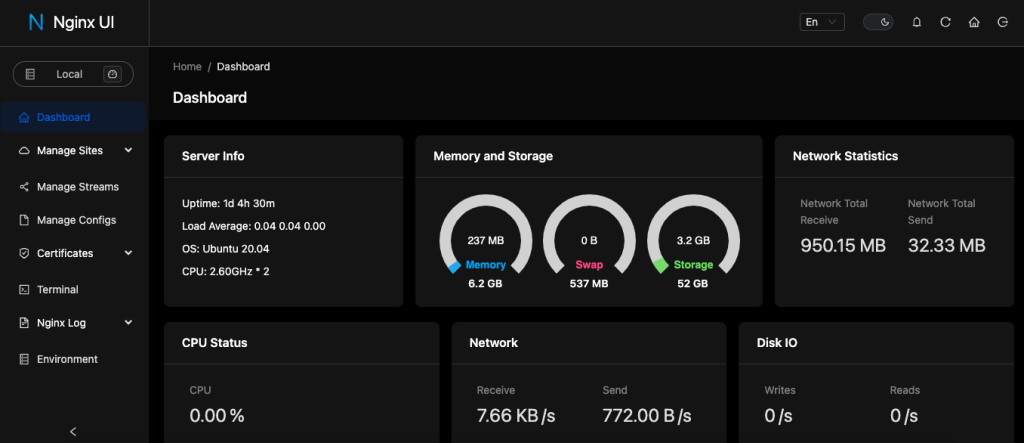
CVE-2026-33032 is a critical security vulnerability that surfaced in the Nginx UI, which is widely used for managing web server configurations. This flaw can potentially allow malicious attackers unauthorized access, enabling them to exploit system weaknesses, manipulate user data, or disrupt server operations. Essentially, it’s a gap in security that could be leveraged to compromise both data integrity and user privacy.
This vulnerability primarily affects versions of Nginx that did not have the latest security patches applied, highlighting the importance of regular system updates. Users were prompted to take immediate action to mitigate risks associated with this flaw.
How was CVE-2026-33032 Discovered?
The discovery of CVE-2026-33032 was credited to a dedicated team of cybersecurity researchers. They were conducting routine audits of the Nginx UI, part of their proactive efforts to identify potential vulnerabilities before they could be exploited by hackers.
Upon discovery, these researchers promptly reported their findings to the Nginx development team. Such collaborations between security experts and software developers are vital in addressing vulnerabilities quickly, preventing potential damage, and maintaining trust within the tech community. The rapid identification and reporting process exemplifies the commitment to cybersecurity within the open-source ecosystem.
Impact of the Vulnerability on Nginx
Who is Affected?
CVE-2026-33032 primarily affects users of the Nginx web server who utilize its UI component for server management. This includes a wide range of users from individual developers running websites to large enterprises that rely on Nginx for their application delivery needs.
Organizations that haven’t applied the latest updates are at the greatest risk, especially those that use custom configurations or extensions, which might not be immediately patched. Anyone deploying Nginx to handle web traffic could potentially face security breaches if this vulnerability is left unpatched.
Potential Consequences for Users
If left unresolved, CVE-2026-33032 could lead to dire consequences for users. Attackers exploiting this vulnerability could gain unauthorized access to sensitive information, alter configurations, or even disrupt web services.
For businesses, this translates to potential data breaches, compromising customer information, and damaging their reputation. Additionally, downtime or server interruptions can result in significant financial losses and customer dissatisfaction.
Tackling this vulnerability promptly is crucial to safeguarding web operations and maintaining the integrity of both private and commercial online environments.
Details of the Nginx UI Patch
How to Apply the Patch
Applying the Nginx UI patch for CVE-2026-33032 is a straightforward process but requires prompt action. Users should first ensure their systems have the latest backup before proceeding with any updates, safeguarding against any unforeseen complications.
To apply the patch, users need to update their Nginx UI to the latest version. This can typically be done using standard package management tools or by downloading the latest release from the official Nginx website. After updating, it’s crucial to restart the Nginx service to ensure the patch is active and the vulnerability is sealed.
Patch Release Notes
The release notes for the Nginx UI patch detail the specific security enhancements applied to address CVE-2026-33032. Notably, this patch strengthens authentication mechanisms, ensuring that unauthorized access attempts are effectively neutralized.
Additionally, the update includes performance improvements and minor bug fixes, contributing to a more stable and secure environment. Users are encouraged to review the complete release notes available on the Nginx blog or repository, which provide further insights into the changes and improvements implemented.
Staying informed and updated is key to maintaining a secure digital infrastructure in the fast-paced world of web services.
Best Practices for Securing Nginx
Regular Security Audits
Regular security audits are a cornerstone of maintaining a secure Nginx environment. These audits involve systematically reviewing configurations, examining logs, and scanning for vulnerabilities. By identifying weak points proactively, you can address potential issues before they become serious threats.
Conducting audits involves both automated tools and manual inspection to ensure comprehensive coverage. Regular audits not only help in discovering overlooked vulnerabilities but also assist in verifying compliance with security policies and standards.
Monitoring and Response Strategies
Effective monitoring and response strategies are essential for promptly identifying and addressing threats in real-time. Implementing robust monitoring tools allows you to detect unusual activities or unauthorized access attempts in your Nginx environment.
These tools should be configured to send alerts and reports, enabling swift action against suspicious activities. Not to mention, having a well-defined incident response plan ensures that your team is prepared to address any security incidents swiftly and effectively, minimizing potential impacts.
Combining proactive monitoring with a clear response strategy strengthens your security posture, keeping your Nginx systems resilient against evolving threats. Regular reviews and updates to these strategies are also critical to adapt to new challenges and technological changes.
Conclusion: Staying Safe with Nginx
Importance of Timely Updates
In the realm of cybersecurity, staying a step ahead often hinges on one simple practice: timely updates. Keeping Nginx and its components up-to-date is not just a recommendation; it’s a crucial part of safeguarding your digital assets against vulnerabilities like CVE-2026-33032.
Updates are how developers address newly discovered vulnerabilities, patch security holes, and enhance performance and stability. By regularly updating your systems, you not only protect against known threats but also capitalize on the latest improvements in security features and functionality.
Ultimately, the responsibility of maintaining a secure environment falls on everyone involved. Whether you’re an individual user or part of a large enterprise, prioritizing updates and following best practices ensures that your Nginx deployment remains robust and resilient against cyber threats, safeguarding your operations and protecting data integrity.